![]() If you’re born before 1990 (and if you’re in IT), you probably grew up with self-signed certificates.
If you’re born before 1990 (and if you’re in IT), you probably grew up with self-signed certificates.
They give you a lovely fake feeling of security, but more than that, they will give users and the IT department horrible stress to configure.
In “days of olde” (early 2000’s), an Exchange server was able to run over http traffic and a certificate was absolutely not required.
Times have changed and so have security protocols. It’s ill-advised to use a self-signed certificate nowadays, as it is equally ill-advised to use a .local domain anymore on your domain controller.
That being said, there’s a couple of ways to fix an expired self-signed certificate on a Windows SBS server. (read first, perform later, you’ll see why)
Lazy mode
aka ‘fix my network’
Open the SBS console, go to the ‘network’ menu and select the ‘Connectivity’ tab.
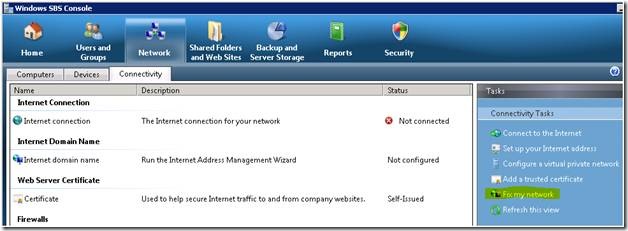
Click ‘Fix my network’ and deselect everything except the certificate error, after this wizard stops scanning.
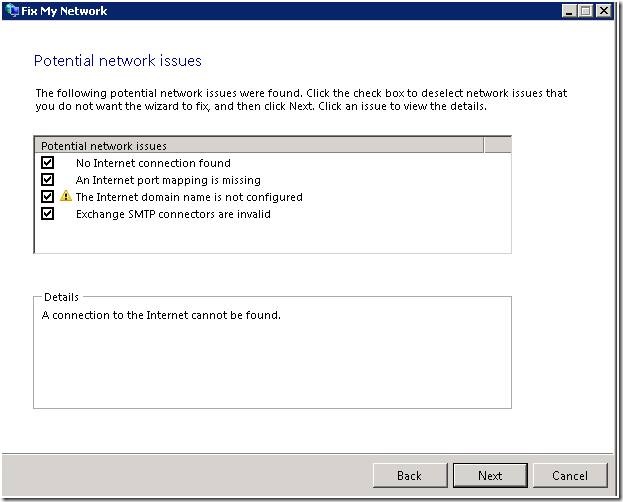
The usual Next-Next-Next will follow and according to Microsoft, you’re good to go.
HOWEVER…
There’s a couple of things that can go wrong here :
- Your certificate contains a custom entry referring to a domain name or subdomain name that wasn’t originally added in the SBS wizard.
You’ll need to perform the manual method for renewing a certificate. See below.
- Your Exchange webmail (https://your_mail_server_ip/owa/) still gives a certificate error, stating your certificate’s still expired.
In this case, your IIS needs to be reminded of the fact that he should use the newly created certificate.
Somewhat easy mode
- Start the ExMngmtnShell (Exchange Management Shell) as Administrator
- type Get-ExchangeCertificate to list the installed certificates
- Match the certificate to the expired certificate (using subject the name and services) from the Console then copy the associated thumbprint
- Type Get-ExchangeCertificate –Thumbprint INSERTTHUMBPRINTHERE | New-ExchangeCertificate | Enble-ExchangeCertificate -services pop,imap,smtp,iis
- Type Y to renew the certificate
- Restart SBS2008/2011 Console or restart server.
- Profit.
Like-a-bawz-mode
 Beautifully explained on http://www.petenetlive.com/KB/Article/0000535, so no need to repeat what Pete already wrote.
Beautifully explained on http://www.petenetlive.com/KB/Article/0000535, so no need to repeat what Pete already wrote.
The main idea here is to use the IIS built-in Certification Authority (certsrv), while manually defining all entries needed in the certificate.
It’s still relatively easy, but requires a lot of steps.
Of all three mentioned methods, this last one is most likely to succeed.
Sources :
- http://www.petenetlive.com/KB/Article/0000535
- https://serverfault.com/questions/526221/renewing-sbs2011-exchange-self-signed-certificate-w-o-changing-home-page-in-ie
- My own meandering experience
